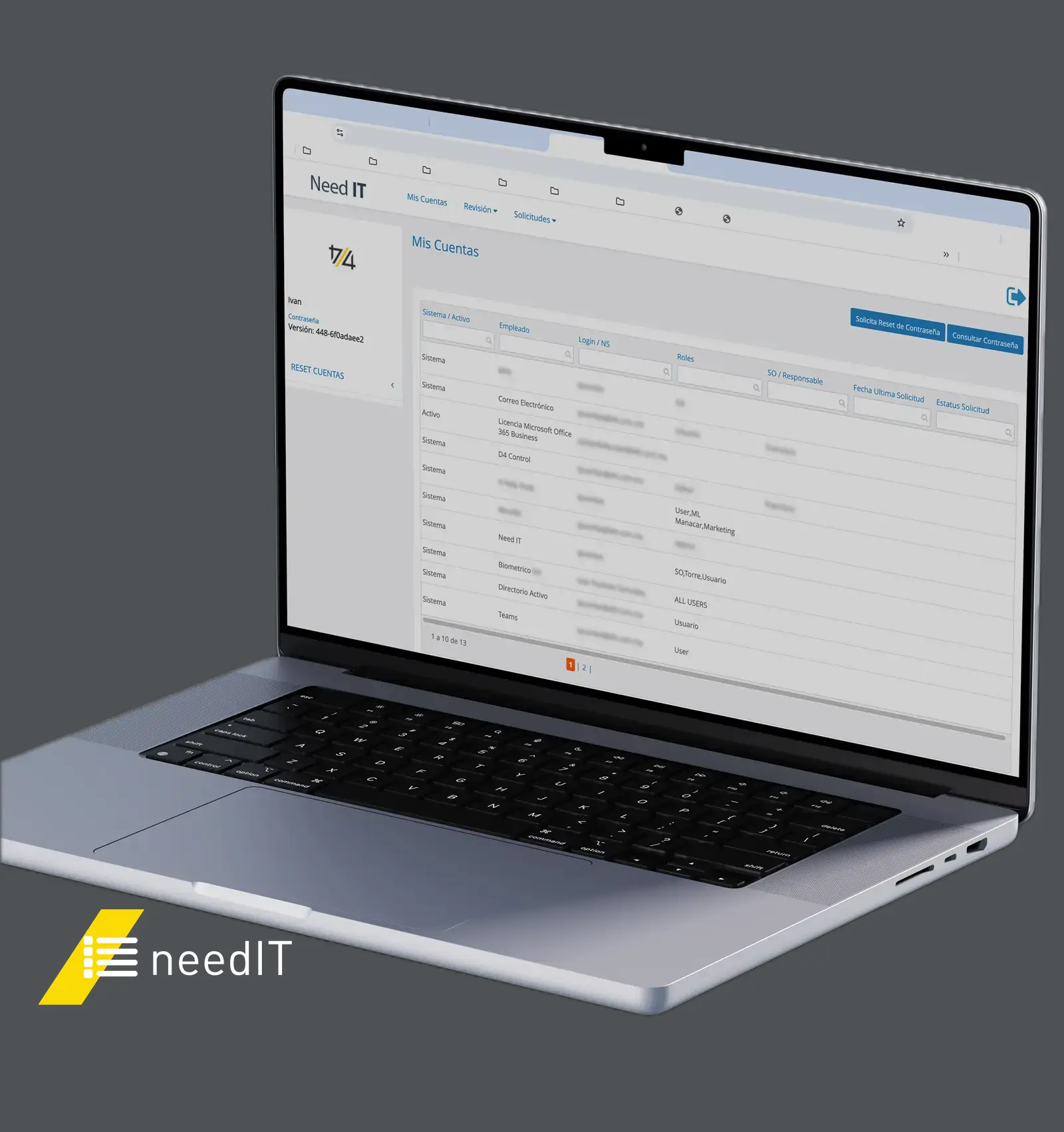
Need IT: access control and security
In today’s environment, mobility and productivity require your team to access their tools from anywhere. However, this flexibility must not compromise the integrity of your organization.
The robust answer to your identity governance and asset management
Guaranteed continuity
Ensure the right people have precise access to the right technological resources, exactly when they need them.
Centralized security
Protect your applications, critical data, and infrastructure through a single, unified platform.
Risk intelligence
Leverage advanced analytics to manage privileges and detect access risks before they become an issue.
Regulatory efficiency
Simplify compliance with security standards and internal controls, reducing administrative complexity.
Key Functionality Modules
01
02
03
04
05
Security, compliance, and support
Designed to detect anomalies and prevent fraud while complying with the most rigorous standards: SOX, HIPAA, PCI DSS, and FTC Safeguards. Manage sensitive data under protocols tailored to your internal control requirements.
01 Availability
99.9% uptime to ensure your operations never stop.
02 Mejores prácticas
Services aligned with the ITIL framework.
03 Critical response
24/7 support for Severity 1 incidents via phone.
04 Specialized support
Help Desk available Monday to Friday (8 am to 8 pm) for efficient incident management.

Support your next major initiative. Schedule an introductory meeting to validate our management model and explore how we can integrate as your trusted technology partner.
México
Av. Insurgentes Sur 1685,
Guadalupe Inn, CDMX.
C.P 01020
Chile
Av. Holanda 099, Oficina 1101, Providencia, Santiago.
Join Our Team
Are you looking for a career opportunity?



